How to Recognize AI Voice Cloning (Simple, Safe Steps for Adults 45+)
By Rado
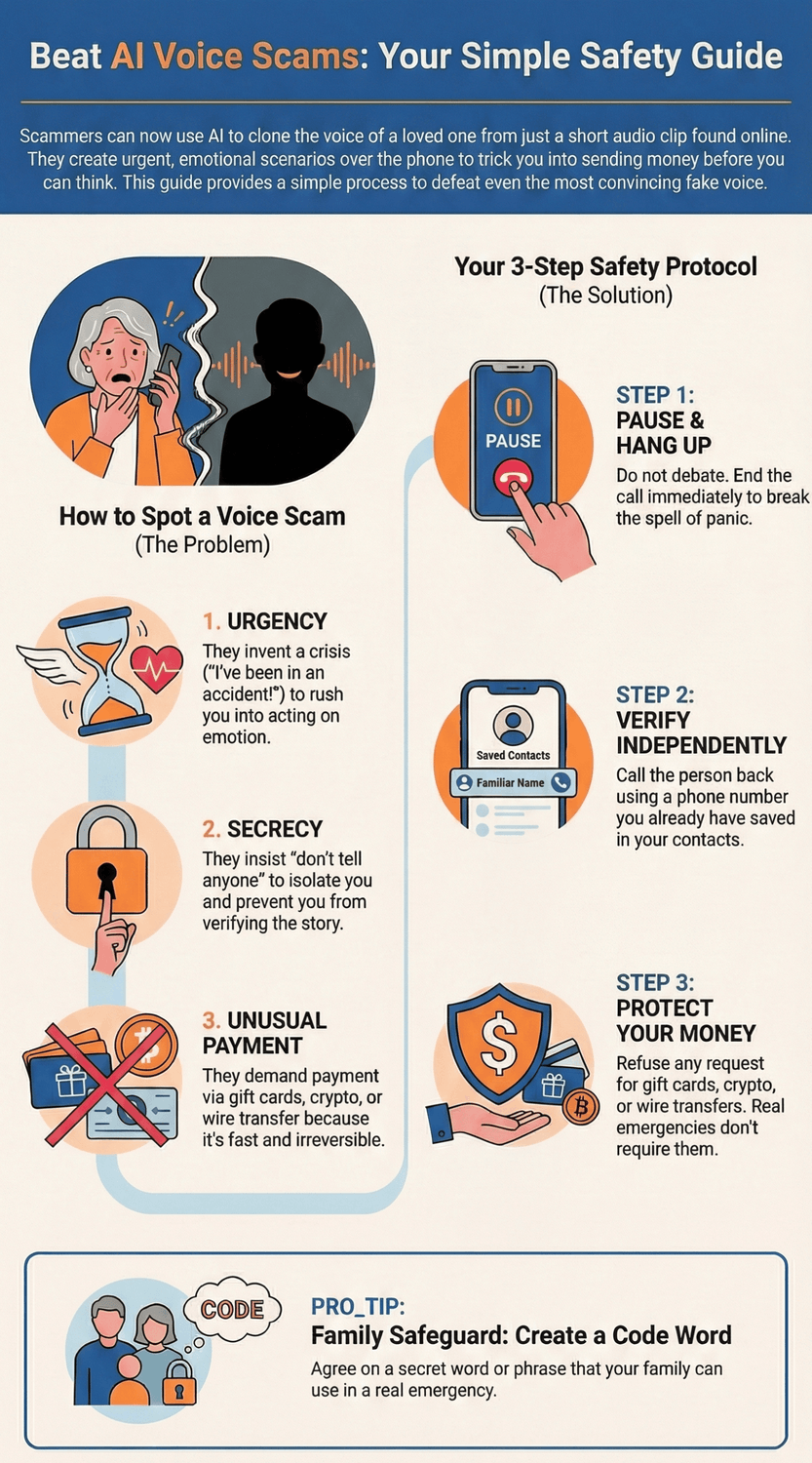
You pick up the phone. It’s your daughter’s voice, shaking, asking for help right now. Your stomach drops. Do you act or verify? That pause could save you thousands. In this guide, we’ll explain what voice cloning is, the reliable signs of a scam, and the exact steps to protect your family using plain language and checklists you can follow in a hurry.
🎧 Prefer to Listen Instead of Read?
Deep Dive into the Podcast Version of this Blog
📺 Watch the Explainer Version of this Blog on YouTube
What is AI voice cloning, in plain language?
You answer the phone and hear your brother asking for help. Same cadence. Same little laugh on the breath. Your heart says yes before your brain catches up. That’s the power of voice cloning: software studies a short sample of someone’s speech and then makes new sentences that sound like them.
So, what’s actually happening? The tool learns patterns in a voice (pitch, pace, accent, pauses) and then generates fresh audio that follows those patterns. It feels real because it mirrors the tiny details our ears use to recognize people. That’s why a good clone can sound close, even when the words are brand new.
Where do scammers get the sample? Often from us. Public Instagram stories, old Facebook videos, YouTube clips, even a voicemail greeting. Once they have a clip, they feed it into a generator and script a story that pushes your buttons. Consumer guidance from the Federal Trade Commission (2024) explains that scammers use cloned voices to make urgent requests for money or information and may spoof caller ID to look familiar. The FTC has also been coordinating responses across agencies and industry to curb voice‑clone abuse FTC (2024).
You might be wondering, can you just “hear” the fake? Sometimes you catch small cues: odd rhythm, over‑formal phrasing, no room noise. But high‑quality clones can fool careful listeners. A NIST (2024) analysis warns that synthetic voices can mislead people and even defeat some biometric checks, which is why process‑based defenses (call‑backs on known numbers, multi‑step verification) matter more than perfect listening.
Why is this showing up now? Tools got faster, cheaper, and easier to use. Law‑enforcement advisories note that criminals are using generative AI to scale fraud and impersonation. The FBI/IC3 (2024) and the FBI (2024) both highlight voice and video cloning in payment scams and account takeovers. Concern is especially high among older adults; AARP (2024) reports rising fear of AI‑related fraud and deepfakes.
So, how should you think about it going forward? Treat your ears as helpful but not final. Use a simple process every time money or sensitive data is involved. Pause. Verify on a known number. Refuse unusual payment methods. These habits beat even the best clone.
The Key Takeaway
Voice cloning is a convincing imitation built from small audio samples.
Your protection isn’t perfect listening.
It’s a repeatable verification routine backed by known numbers and clear payment rules.
How common is it, and why now?
You get a late call. A familiar voice says there was an accident and needs help right away. Your chest tightens. Do you send money first and check later? That reaction is exactly what scammers count on, and it is getting more common because the tools are getting easier to use.
So, how widespread is this? Consumer agencies and researchers say deepfakes are moving from niche to everyday. In the United Kingdom, a national Ofcom poll found that 43% of adults had seen at least one deepfake in the previous six months Ofcom (2024).
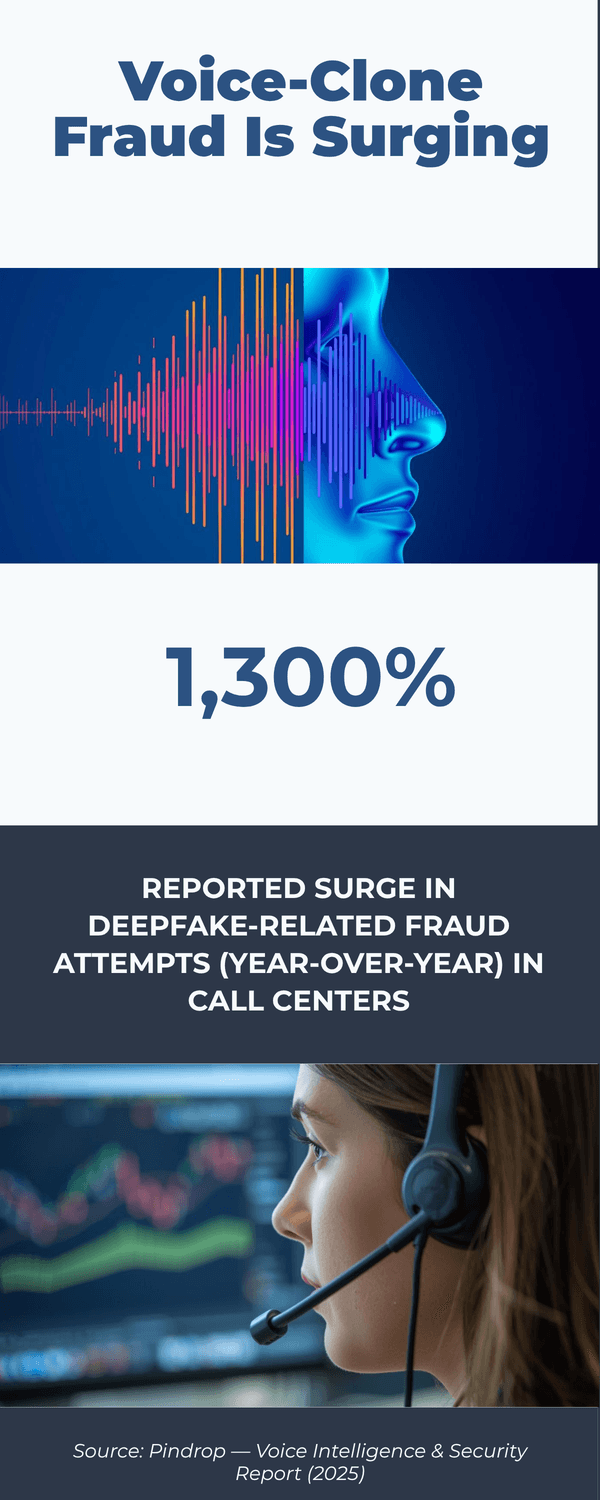
Contact centers report rising synthetic voice activity and large fraud exposure tied to AI‑assisted calls Pindrop (2025), with projections that deepfake‑related fraud could jump by more than 150% this year Pindrop (2025). In the United States, federal warnings continue to highlight AI‑driven impersonation in scams and credential theft FBI IC3 (2024) and even the impersonation of senior officials through AI‑generated text and voice messages FBI (2025).
Why now? Three simple reasons. First, audio samples are everywhere. Short voice clips live on Instagram, Facebook, YouTube, and voicemail greetings. Second, the cost of cloning has dropped while quality has improved. You no longer need a studio‑length sample or special hardware. Third, criminals scale fast. One convincing script can be reused with many targets, and caller ID spoofing helps it pass a quick glance FTC (2024).
You might be wondering, are older adults singled out? Sadly, yes. High‑pressure situations, secrecy, and family trust can override caution. Advocacy groups are pushing for stronger protections and curb spam robocalls that open the door to these scams AARP (2025). And real‑world cases show how persuasive these calls can be when fear is high People Magazine (2025).
What does this mean for you? Expect more attempts across phone calls, voice notes, and even messaging apps that allow audio. Expect better acting and more believable background noise. Expect a second impostor joining the call as a “lawyer” or “bank agent”.
Now the good news. While detection is improving, your best defense is still simple habits. Save trusted numbers. Refuse unusual payment methods. Call back on a number you already know. Report suspicious attempts so patterns get flagged faster.
The Key Takeaway
It is common enough to plan for.
The rise comes from easy access to voice samples, cheap and good cloning tools, and scalable fraud scripts.
Do not rely on your ears alone.
Rely on a short pause and a verified call‑back before you move money or share sensitive information.
What does a real voice‑clone scam sound like?
It often starts in the first three seconds. A shaky voice you know says there’s been an accident. You hear traffic, maybe a nurse in the background. Your pulse jumps. Do you help first and check later? That snap decision is what the scammer wants.
Most voice‑clone calls follow a script that pushes fear and speed. The story is rushed. The request is urgent. You are told to keep it secret. Then comes payment that is hard to reverse.
What does this actually sound like? You may hear a familiar greeting and a breathy pause, then a fast story: “I’m at the police station. Please don’t tell Mom.” A second person may jump in as the “officer” or “lawyer” to add pressure. Caller ID can match a saved name because spoofing is common. Scammers often insist on gift cards, crypto, or a wire transfer because those are fast and final. This pattern appears again and again in consumer alerts from the Federal Trade Commission (2024) and in law‑enforcement notices from the FBI IC3 (2024).
Listen for the emotional throttle. The voice may sound teary, short of breath, or oddly flat between bursts of panic. There might be strange turns of phrase that your loved one would not use. Background noise can be too perfect or looped. None of these prove a clone, but together they should slow you down. The FCC (2024) warns that spoofed numbers and synthetic voices are often paired to make the call feel real.
You might be wondering, what if it really is an emergency? That’s a fair question. It’s normal to feel torn. Here is a simple rule you can trust under stress: help after you verify. Hang up. Call back on a number you already saved. If you can’t reach them, call a second relative or friend. Real emergencies survive a brief check. Scams don’t.
Want a quick mental checklist while you listen?
Is there urgency plus secrecy plus unusual payment? Treat it as a scam.
Are they stopping you from calling back on a known number? Pause.
Are they asking for codes, transfers, or gift cards right now? Stop.
Real‑world cases show how convincing these calls can be when fear is high. News reports describe parents paying thousands after hearing a cloned child’s cry before they could think clearly, which is why agencies stress a call‑back routine and refusal of irreversible payments AARP (2024).
The Key Takeaway
A voice‑clone scam sounds fast, scared, and secretive, often with a second “authority” and payment that cannot be reversed.
Your defense is calm timing.
Hang up, verify on a known number, and never move money under pressure.
Which red flags should you trust over your ears?
You hear your niece’s voice whisper, “Please don’t tell anyone—just help.” Your body reacts before your brain. That’s normal. It’s also why scammers lean on speed and secrecy. When your ears are unsure, these red flags are the ones to trust every time.
Here’s the short version. Urgency, secrecy, and unusual payment methods form the classic scam triangle. If all three show up, stop. The Federal Trade Commission (2024) and FBI IC3 (2024) both warn that impostors try to rush you, isolate you, and push you to pay in ways that are hard to reverse.
Let’s break the red flags down so you can spot them fast:
1) Urgency that blocks thinking
“Right now.” “You have 10 minutes.” “Don’t hang up.” Pressure is a tool. Real helpers let you verify. Government guidance is clear: slow down and independently confirm using a number you already saved (FCC, 2024; FTC, 2024).
2) Secrecy or isolation
“Don’t tell Mom.” “Keep this between us.” “If you call the bank, it will make things worse.” Why the hush? Isolation keeps you from hearing a second opinion. Agencies advise switching channels and doing a quick call‑back on a known number (FTC, 2024).
3) Unusual or irreversible payment
Gift cards, crypto, wire transfers, courier cash pickups. These are favorites because once the money moves, it is hard to get back. Banks and regulators repeat this warning across alerts (FTC, 2024; FinCEN, 2024).

4) Requests for codes or access
“Read me the code you just got.” “Share your screen.” “What’s your online banking password?” No real bank or tech support asks for authentication codes in a cold call. The FBI (2024) and many banks warn that one‑time codes are keys to your accounts.
5) Refusal to let you call back
Scammers push you to stay on the line and block a call‑back. A simple test: hang up and call the person or organization using a number you already saved. Real emergencies survive a brief check. Scams don’t (FTC, 2024).
6) Story changes under gentle questions
Ask for a middle name, a detail from a recent family event, or the family code word. Do they dodge? Do details shift? That wobble matters. Advocacy groups encourage families to set a code word and rehearse a quick verification plan (AARP, 2024).
You might be wondering, what if I’m wrong and someone really needs help? That’s a fair concern. It’s normal to feel torn. Remember: you can be kind and still verify. Offer to call right back. Then use a trusted number from your contacts, not the incoming call or a number they give you.
Want a pocket checklist? Try this:
Urgency + secrecy + unusual payment = stop.
Never share codes, passwords, or screen access.
Hang up and call back on a saved, known number.
Refuse gift cards, crypto, or wires.
Log the time and number for reporting.
The Key Takeaway
Trust patterns, not your ears.
If the call brings speed, secrecy, and hard‑to‑reverse payment, it’s safer to pause, verify on a known number, and protect your money.
What should you do during a suspicious call? (The Pause Protocol)
You pick up. A familiar voice pleads for help. Your chest tightens. That first rush is human. It is also the moment to switch to a simple script that protects you.
Pause. Verify on a number you already trust. Refuse any fast or private payment. This routine works even when a clone sounds perfect.
Step 1: Take a breath and buy time
Say, “I am here. I am calling you right back.” A 10 second pause breaks the panic loop so you can think.
Step 2: Hang up
Do not debate on the line. End the call. The Federal Trade Commission advises you to stop and confirm independently before you act.
Step 3: Call back using a saved contact
Use the number in your phone’s contacts or a recent text thread you started. Do not use any number the caller gives you. The FCC and FTC both recommend independent call‑backs.
Step 4: If no answer, do a two person check
Call a second family member or friend. Ask them to reach the person. Real emergencies survive a brief verification.
Step 5: Use your family code word or a challenge question
Ask for the agreed code word or a detail only your family knows. No code. No action. If you have not set one yet, add it after you read this section.

Step 6: Refuse irreversible payments
Never send gift cards, crypto, wire transfers, or cash pickups. These are top scam tools. The FTC and FBI IC3 warn that once money moves by these methods, recovery is unlikely.
Step 7: Protect your accounts
Do not share one time codes, passwords, or screen access. Banks will not ask for codes on a cold call. If you shared anything, contact your bank right away and change passwords.
Step 8: Capture details
Write down time, the number that called, and what was said. Take screenshots of texts. These help your bank and investigators.
Step 9: Report it
Alert your bank or credit union. File a report with your local police. In the United States, submit to the FBI Internet Crime Complaint Center. In the United Kingdom, report to Action Fraud. In other countries, use your national cybercrime portal or consumer protection agency.
Step 10: Tell your family
Let relatives know what happened so they can spot the same script. Scammers often re‑try numbers from the same household.
You might be wondering, what if it is truly urgent. That is a fair worry. Remember this line: “I am calling you back on your saved number right now.” Real emergencies allow it. Scams do not.
One minute drill you can practice
Breathe. Hang up. Call back on a saved number. If no answer, call a second relative. Refuse gift cards, crypto, or wires. Save the details. Report.
The Key Takeaway
You do not need perfect ears.
You need a short script.
Pause.
Verify on a known number.
Refuse irreversible payments.
Document and report.
This routine protects you when emotion is high.
How do you set up family safeguards that actually work?
Imagine a Sunday lunch. You take two minutes to agree on a simple plan, then go back to dessert. That tiny prep can save you thousands on a stressful weekday when a cloned voice calls.
Write a mini‑plan. Share it with the people who will pick up the phone. Practice it once. Review it twice a year. Real protection is a routine everyone remembers when nerves are high.
1) Create a family code word
Pick a non‑obvious word or short phrase that is not used online. Keep it ordinary, like “pepper tree” or “map drawer.” Decide that any urgent request without the code is a no. Guidance from consumer agencies backs this simple step and the pause‑and‑verify habit you will pair with it (FTC, AARP).
2) Add a two‑step challenge
If you forget the code word, use a fallback only close family would know. Example: “What nickname did Grandpa use for you?” No correct answer, no action. The idea is to slow the moment and force a real connection.
3) Build a trusted contact list
On paper and in your phone, list: immediate family, a neighbor, one close friend, your bank’s official number, and your doctor’s office. Label them “Trusted.” Agree to use these numbers only, not any number read to you on a call. The FCC and FTC both recommend independent call‑backs on known numbers.
4) Write a 60‑second verification script
Post a note by the phone:
Breathe. Hang up.
Call back on a saved number.
If no answer, call a second relative.
Refuse gift cards, crypto, or wires.
Save details. Report.
Practice the script out loud. You might feel silly for one minute. You will feel grateful later.
5) Set payment guardrails
Agree on a house rule: no irreversible payments under pressure. That means no gift cards, crypto, wire transfers, courier cash. Banks and law‑enforcement warn these are the top scam rails (FTC, IC3).
6) Share the plan where it matters
Make sure teens, grandparents, and caregivers have the code word and the script. Save the plan as a photo in your favorites. Put a printed copy in your wallet. Create a family chat message with the plan pinned at the top.
7) Lock down voice samples
Tighten who can see your videos and voice notes. Use neutral voicemail greetings. Ask relatives not to post long, high‑quality clips of you. A smaller public voice footprint means fewer raw materials for cloners (NIST).
8) Schedule a six‑month review
Add a calendar reminder for January and July. Update numbers. Change the code word. Role‑play one quick call. Many families stop at “we should.” The review makes it real.
9) Add account safety basics
Turn on two‑factor authentication for your main email and bank. Set transaction alerts. Use unique passwords. If anyone ever shared a code or password in a call, change it today and tell the bank (FBI IC3).
You might be wondering, will everyone remember in a panic? That’s a fair worry. It’s normal to freeze. That’s why you practice once and keep the plan simple. The goal is not perfection. It’s a short, repeatable routine that buys you time to verify.
Quick setup checklist
Pick a code word and a fallback question.
Save a trusted contact list on paper and in your phone.
Post the 60‑second script by the phone and in a family chat.
Turn on banking and email alerts.
Put a six‑month reminder on your calendar.
The Key Takeaway
A small, shared routine beats a perfect ear.
Code word, call‑back on saved numbers, no irreversible payments, and a six‑month review.
Simple steps, strong protection.
Can you tell a clone by listening? (Limits of human detection)
You answer a call on speaker while making coffee. It sounds like your son. Same rhythm. Same quick inhale before he speaks. Your gut says it is him. But is your ear enough?
Careful listening can help, but your ear alone is not reliable. High‑quality clones now copy pitch, pacing, tone, and even breathy texture well enough to fool thoughtful people. That is why officials urge process‑based checks instead of “I can just tell.” The National Institute of Standards and Technology (2024) describes synthetic voice risks that can defeat human judgment and some biometric checks, and the Federal Trade Commission (2024) advises independent verification using known numbers.
So, what can your ears still notice? Think of these as helpful clues, not proof:
Odd rhythm or timing. Slightly off pauses, words that run together, or a “metronome” feel.
Mismatch between words and emotion. Serious news with flat affect, or casual updates with overdone drama.
Over‑formal phrasing. Sentences your loved one would never say that way.
Breaths and room noise. Either missing entirely or sounding the same across the whole call.
Compression artifacts. A faint metallic edge or watery tail on certain syllables.
You might be wondering, can background sounds prove it is real? Not really. Scammers often add hospital beeps, traffic, or office chatter to sell the story. Those layers can be pre‑recorded or generated. Ask yourself: do the sounds change naturally as the person moves the phone? Or do they loop? Still, treat audio cues as a reason to pause and verify, not as a final verdict.
What about asking questions only they would know? Good idea, with limits. If a criminal used your social media, they might know a pet’s name or birthday. Use a code word agreed in advance or a two‑step challenge that is not online. If they dodge or stall, that is a signal to hang up and call back on a saved number.
Are there apps that detect clones for you? Some tools can flag patterns in recorded audio, but real‑time accuracy is mixed and false alarms do happen. Even researchers running lab tests point out that detection gets harder as cloning improves, so you should not wait for a perfect app to protect you. Both NIST (2024) and FTC (2024) stress layered defenses: known‑number call‑backs, refusal of irreversible payments, and strong account hygiene.
One useful habit is to change channels. If a voice note on WhatsApp asks for money, switch to a phone call using a number you saved months ago. If a call feels off, hang up and text a family chat you already use. Real emergencies survive a short check. Scams do not.
The Key Takeaway
Your hearing is a good early warning, not a final test.
Use clues to slow down, then follow your routine: known‑number call‑back, code word or challenge question, and “no irreversible payments” under pressure.
How can you reduce your public voice footprint?
Picture scrolling your old Facebook videos and hearing a birthday toast from years ago. Sweet memory for you. Gold mine for a scammer. A smaller public voice footprint means fewer raw materials to clone.
Tighten what you share. Clean up old clips. Use neutral voicemail. Ask others to be careful with your voice. These small steps lower your risk without killing your fun online.
1) Review your public profiles
Open Facebook, Instagram, YouTube, TikTok, and LinkedIn. Set older videos to “friends,” “private,” or “unlisted.” Remove clips where your voice is clear and long. The Federal Trade Commission recommends regular privacy checkups and limiting what is public.
2) Trim long voice posts
Short birthday wishes are less useful to cloners than a five‑minute speech. Keep public audio short. Share longer clips only in closed groups.
3) Update your voicemail greeting
Use a neutral line like, “You’ve reached Chris. Please leave a message.” Skip personal details and long recordings.
4) Ask family to share wisely
Kids and relatives often post the longest, clearest videos of us. Kindly ask them to keep your voice clips to friends‑only or to send them privately. Advocacy groups encourage families to reduce public data that can be reused in scams AARP.
5) Mind live streams and webinars
If a session will be posted publicly, ask the host to edit out long Q&A audio or to share only highlights. Request “unlisted” rather than widely public when possible.
6) Audit video tags and mentions
Search your name on YouTube, Facebook, and Instagram. Untag or request removal where your voice is clear. Many platforms provide reporting tools for unwanted content; start there.
7) Lock down messaging app settings
In WhatsApp, iMessage, and Telegram, turn on privacy options and auto‑delete for voice notes in sensitive chats. Share fewer voice notes with new contacts.
8) Be careful with AI voice features
Some apps offer voice training or custom voices. Use these only with services you trust. Avoid uploading long reference recordings unless you are sure how they are stored and used. The National Institute of Standards and Technology cautions that voice data can be reused beyond the original context.
9) Remove old, high‑quality audio
Podcasts, interviews, speeches. If you no longer need them public, unlist or delete. Keep a private copy for yourself.
10) Do a seasonal cleanup
Put a calendar reminder for January and July. Five minutes per site. Small, steady cleanups beat one big purge.
You might be wondering, do I have to scrub everything? No. It’s normal to share some moments. The goal is to make it harder to collect clean, long samples of your voice. Think “less and shorter,” plus tighter audience controls.
Quick checklist
Set old videos to private or unlisted.
Use a short, neutral voicemail greeting.
Ask family to limit public voice clips.
Review tags and request removals.
Add a twice‑a‑year privacy reminder.
The Key Takeaway
You don’t need to vanish online.
Just reduce long, public voice clips and tighten who can see them.
A smaller footprint gives cloners less to work with.
What should you do if you already paid or shared info?
It happens. Fear is fast. If money moved or you shared a code, don’t feel ashamed. Move quickly and follow a short, ordered plan to limit the damage and improve your chances of recovery.
1) Contact your bank or credit union immediately
Explain that you were targeted by an AI voice‑clone (imposter) scam. Ask them to freeze the account, attempt a recall, or flag the transaction as fraud. Many institutions can help if you act fast. Keep the case number.
2) If you sent a wire, crypto, or gift cards
Wire: Request a recall and file a fraud report. Provide dates, amounts, and receiving details.
Crypto: Contact the exchange right away with transaction IDs. Some platforms can freeze assets if they reach them in time.
Gift cards: Call the card issuer’s fraud line and give the numbers and receipts. Some issuers can halt redemption if you report quickly. See FTC – Gift Card Scams for issuer contacts.
3) Lock down your accounts
If you shared any one‑time code, password, or gave screen access, immediately:
Change passwords for email, banking, and cloud storage.
Revoke unrecognized devices or sessions.
Turn on two‑factor authentication.
Banks and agencies stress that codes grant access like a key; change them fast (FBI IC3).
4) Save every record
Screenshots, call logs, voicemails, receipts, gift card numbers, wallet addresses. Write a timeline. These help banks, police, and insurance.
5) File official reports
Police report: Your local department (helps with bank and insurer requests).
National cyber/fraud portal:
United States: FBI Internet Crime Complaint Center
United Kingdom: Action Fraud
European Union: report via your national police/cybercrime unit.
Canada: Canadian Anti‑Fraud Centre
Use confirmations to update your bank case.
6) Place alerts and consider freezes
Turn on bank and card transaction alerts. Consider a credit freeze or fraud alert with credit bureaus in your country to block new‑account fraud. In the U.S., request freezes with Equifax, Experian, and TransUnion. In the U.K./EU, use your national credit reference agencies.
7) Warn your family
Share a short message in your family chat: what happened, what number called, and the plan going forward. Scammers often re‑target the same household.
8) Review and reset your defenses
Add a family code word and the call‑back routine. Shorten your public voice footprint (see earlier section). Update passwords and enable two‑factor authentication everywhere it matters.
Is there any chance to get the money back? Sometimes. Speed and documentation help. Banks are more likely to assist when you act within hours, not days, and when you provide a clear timeline and proof.
Quick recovery checklist
Call your bank now; ask for a freeze/recall and get a case number.
If wire/crypto/gift cards, contact the provider with all details.
Change passwords and turn on two‑factor authentication.
Save screenshots, logs, and receipts.
File police and national fraud reports; share case numbers with your bank.
Alert family; activate your verification plan.
The Key Takeaway
Don’t freeze.
Act.
Fast calls, saved evidence, and official reports give you the best chance to recover funds and prevent repeat attacks.
Which tools and settings can help?
Picture your phone as a front door. A good lock, a peephole, and a porch light will not stop every thief, but they make a huge difference. Your devices and bank already have simple tools that do the same.
Here’s the short version. Use call filters, tighten account alerts, and set payment guardrails. These reduce noise, buy time, and stop money from moving in a panic.
Phone protections you can turn on in minutes
Silence unknown callers / send to voicemail. Let unfamiliar numbers go to voicemail so you can verify calmly. Both iOS and Android offer built‑in call silencing and spam filtering features. The Federal Communications Commission explains why screening unknown calls reduces scam risk.
Filter suspected spam. Enable your phone’s spam filter and your carrier’s free blocking tools. Many carriers flag “Scam Likely” calls by default.
Block and report. After a suspect call or text, block the number and report it as spam. Reports help carriers improve filters.
Do Not Disturb with favorites. Set an exception list for immediate family and key contacts. You still screen strangers while real emergencies get through.
Messaging and email habits that lower risk
Turn off link previews from unknown senders. Previews can load tracking or look convincing.
Move to a known channel. If a WhatsApp voice note asks for money, switch to a call using a saved number. Agencies advise independent call‑backs on known numbers (FTC).
Bank and wallet settings that stop losses
Turn on transaction alerts. Get instant notifications for card charges, transfers, or Zelle‑type payments. Fast alerts let you freeze activity quickly.
Set daily transfer limits. Ask your bank to lower default limits for wires and instant transfers on consumer accounts. Limits buy you time if someone pressures you.
Add a second approval for large moves. Some banks let you require a second confirmation by another device or person.
Use strong sign‑in. Unique passwords plus two‑factor authentication on banking and email. The FBI IC3 and FTC stress that one‑time codes should never be shared on a call.
Identity and privacy helpers
Credit alerts or freezes. Consider a fraud alert or credit freeze to block new‑account fraud.
Account activity dashboards. Regularly review sign‑ins and connected devices for your email and cloud accounts; sign out of anything you do not recognize.
Tighten social privacy. Reduce long, public voice clips and set old videos to private or unlisted. Guidance from AARP and FTC encourages seasonal privacy checkups.
Simple automations that help under stress
Create a Trusted Contacts group in your phone. Give that group its own ringtone. In a crisis, you know it is really them.
Save a note in Contacts for each family member with the agreed code word and your call‑back script.
Add a calendar reminder twice a year to test alerts, review limits, and practice the one‑minute drill.
Will these block every scam? No tool is perfect, and scammers change tactics. That is normal. Tools are there to slow things down and protect your money while you verify.
Quick setup checklist
Turn on call silencing and spam filtering.
Enable bank alerts, lower transfer limits, add two‑factor authentication.
Create a Trusted Contacts group and special ringtone.
Schedule a six‑month privacy and security check.
The Key Takeaway
Use your phone and bank like safety gear.
Filters and alerts reduce pressure, while limits and two‑factor authentication keep money from moving until you verify on a known number.
How are banks and companies fighting back and what it means for you
You call your bank and they ask extra questions before moving money. It feels slower. Is that a problem or protection? In a world of cloned voices, the “slow‑down” you feel is part of the defense.
Here is the short version. Financial institutions and service providers are adding layered checks to spot unusual activity and defeat synthetic voices. You will notice more call‑backs, more identity tests, and more alerts. It can feel inconvenient. It is there to guard your accounts.
1) Stronger verification and “liveness” tests
Companies are adding tests that confirm a real person is present, not a recording or a clone. That might include random prompts, brief video checks, or movement cues. Guidance from the National Institute of Standards and Technology (2024) urges layered, risk‑based identity verification rather than relying on a single biometric like a voiceprint.
2) Smarter fraud monitoring
Banks use analytics to flag out‑of‑pattern transfers, new payees, or rapid changes to limits. When the pattern looks risky, they trigger holds or a manual review. The FBI IC3 encourages consumers to cooperate with these checks because they often stop losses mid‑flow.
3) Call‑back and secure‑channel rules
Many institutions will not act on high‑risk requests inside one call. They insist on a call‑back to a number on file or a message inside the bank’s app. The Federal Trade Commission and Federal Communications Commission both recommend independent call‑backs on known numbers; banks are building that advice into policy.
4) Payment guardrails by default
More providers are lowering default transfer limits, adding cooling‑off periods for first‑time payees, and requiring a second approval for large moves. Treasury’s FinCEN advisory (2024) highlights deepfake‑enabled fraud trends and encourages stronger controls and staff training.
5) Education and real‑time warnings
You will see in‑app banners and pop‑ups that ask, “Were you told to buy gift cards?” or “Did someone call you to move money?” These friction points are intentional. They interrupt the panic cycle that scammers create. Consumer groups like AARP support these prompts because they help people pause and verify.
Will this slow me down when I truly need to act fast? Sometimes. That is a fair trade. Those extra thirty seconds are there to save you hours on the phone and weeks of cleanup. If you know what to expect, the friction feels less annoying and more like a seat belt.
How to work with these defenses
Keep your contact info current so call‑backs reach you quickly.
Turn on account alerts so you can approve or deny activity in seconds.
Use your bank’s secure app for messages and confirmations.
Be ready for a brief video or liveness prompt on high‑risk changes.
Thank the clerk who slows down a risky transfer. They likely saved you money.
The Key Takeaway
Expect a little more friction.
It is by design.
Call‑backs, liveness checks, alerts, and limits are there to beat voice clones.
When your bank slows down a risky request, it is protecting your balance, not blocking your day.
To conclude...
You do not need perfect ears to stay safe. You need a small routine you can use when emotions run hot. Pause. Hang up. Call back on a number you already trust. Refuse gift cards, crypto, and wire transfers under pressure. Set a family code word and rehearse a one‑minute drill. These habits turn a scary moment into a controlled one.
You might be wondering, will this take a lot of time? Not really. Ten minutes to set your plan. One minute to practice. Thirty seconds to verify during a call. That trade protects your savings and your peace of mind.
🎓 Your "Tech Dignity" Toolkit
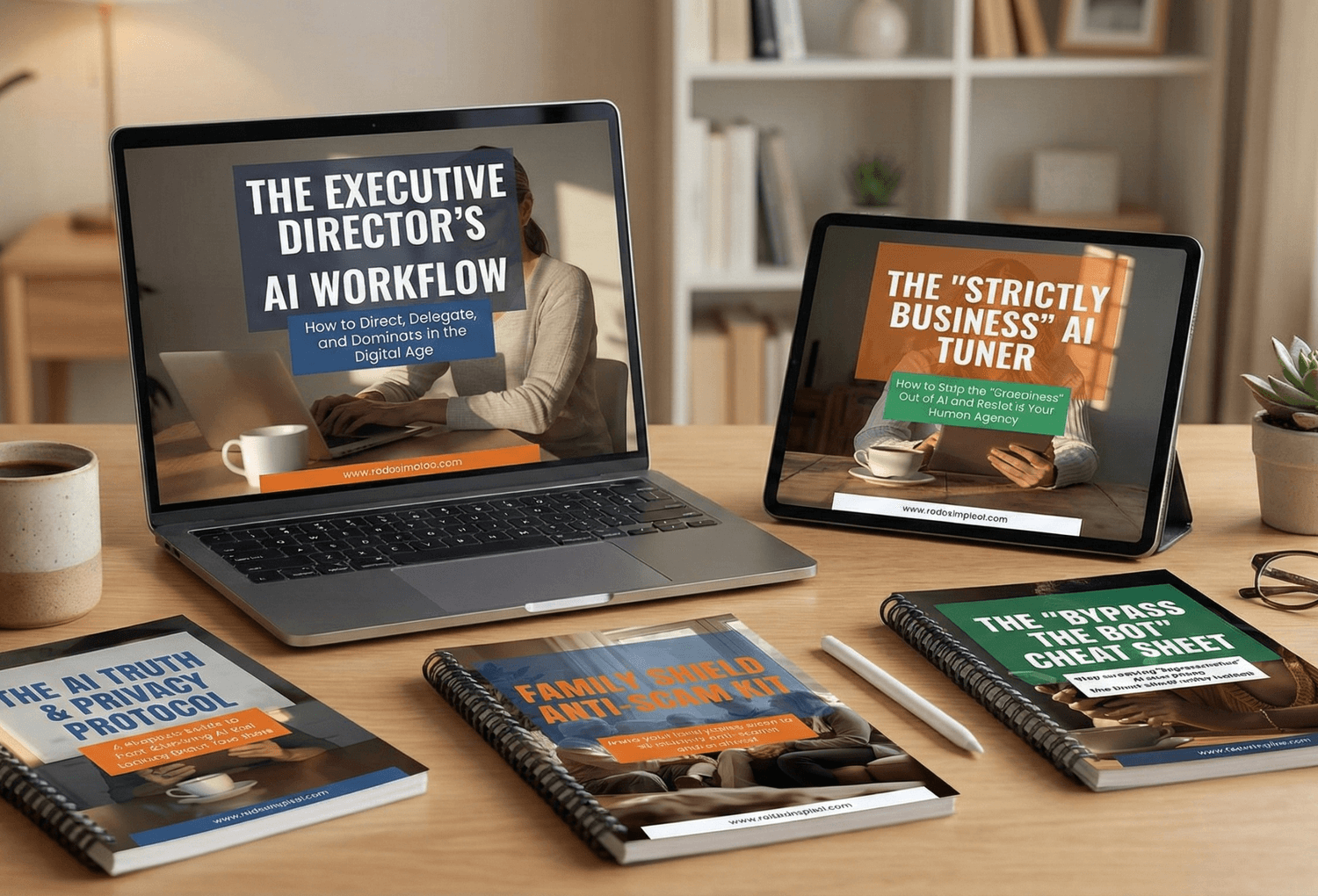
Ready to stop surviving the AI era and start owning it? I’ve built a library of resources specifically designed to help you stay safe, stay professional, and stay in control. Whether you want to fix a specific problem or master the whole machine, start here:
[FREE] The "Bypass the Bot" Bundle: Stop screaming at automated phone menus. Get the secret codes and scripts to reach a human every time. Download for FREE Here
Secure Your Family: Protect your loved ones from AI voice clones and deepfake scams with the Family Shield Anti-Scam Kit. Get Protected for $9
Upgrade Your Career: Use my "Strategy Sandwich" method to delegate grunt work to AI while keeping your professional edge with the Executive Director’s AI Workflow. Reclaim Your Time Here
Lock Down Your Privacy: Interrogate the "black box" and secure your data with the AI Truth & Privacy Protocol. Secure Your Data Here
Tame the Machine: Strip the "creepy" fake empathy out of AI and turn it into a silent tool with the "Strictly Business" AI Tuner. Take Control Here
The Ultimate Shortcut: Want the entire library? Secure your digital future with the Complete Mastery Collection (all products bundled for about 57% off). Get the Full Collection Here
Frequently Asked Questions
Q1) Can I tell a cloned voice just by listening?
Listening can help, but your ear alone is not reliable. High quality clones can fool careful people. Use a call‑back on a saved number and a family code word instead. See NIST (2024) and FTC (2024).
Q2) What should I do in the moment if I get a scary call?
Say you will call right back. Hang up. Call the person using a number in your contacts. If no answer, call a second relative. Refuse any request for gift cards, crypto, or a wire. Guidance from FTC (2024) and FCC (2024) supports independent verification.
Q3) Are older adults targeted more often?
Imposter scams often exploit trust, urgency, and secrecy inside families. Advocacy and law‑enforcement groups warn that criminals increasingly use AI voices in these schemes. See AARP (2024) and FBI IC3 (2024).
Q4) How do I set up a family code word that works?
Pick a simple phrase that is not online and promise to use it only in real emergencies. Pair it with a two‑step challenge question as a backup. Consumer guidance recommends these checks to stop impulse payments FTC (2024).
Q5) What if the caller ID matches a saved contact?
Spoofing is common. Do not trust the screen alone. End the call and dial the person back using the number you already saved. See FCC (2024).
Q6) Are there apps that can detect voice clones for me?
Some tools can flag recorded audio, but real‑time accuracy is mixed and false alarms happen. Officials advise process‑based defenses while detection improves NIST (2024).
Q7) I already sent money. What now?
Call your bank right away to request a freeze or recall, save evidence, and file official reports. In the U.S., use the FBI Internet Crime Complaint Center (IC3). In the U.K., report to Action Fraud. More guidance: FTC – Gift Card Scams.
Q8) How can I lower the chance my voice gets cloned?
Reduce long, public clips of your voice, tighten social privacy settings, and use a short, neutral voicemail greeting. Seasonal privacy checkups help FTC (2024) and AARP (2024).
Q9) Why do banks make me pass extra checks now?
Banks add call‑backs, liveness checks, alerts, and lower transfer limits to catch fraud. It can feel slower, but it protects your balance. See FinCEN (2024) and FBI IC3 (2024).
Q10) What are the three fastest red flags I should trust?
Urgency, secrecy, and unusual payment. If you hear all three, stop. Hang up and call back on a known number. See FTC (2024).
Sources
Federal Trade Commission — Fighting Back Against Harmful Voice Cloning (2024).
Federal Trade Commission — How to Avoid a Scam (2024).
Federal Communications Commission — Voice Cloning and Robocalls (2024).
FBI Internet Crime Complaint Center (IC3) — Public Service Announcement: AI‑Enabled Scams (2024).
National Institute of Standards and Technology — AI 100‑4: Reducing Risks Posed by Synthetic Content (2024).
AARP — AI Scams: What to Watch For (2024).
FinCEN, U.S. Treasury — Advisory: Deepfake Fraud Trends (2024).
Action Fraud (UK) — Report Fraud and Cyber Crime (accessed 2025).
Canadian Anti‑Fraud Centre — Report Fraud (accessed 2025).